Trust your assets, fuel your AI: Everything new in Axonius Asset Cloud

Hadas Schlessinger
Director of Product Management, Axonius

Teju Shyamsundar
Principal Manager, Product Marketing, Axonius

Shira Ben Porat
Principal Product Manager, Axonius

The actionability era set a new bar for asset intelligence. Visibility was just the first step. Security teams needed to turn that visibility into action, faster, across every program.
As automation scales and AI becomes embedded in security operations workflows, a new, potentially even tougher challenge has surfaced: what happens when the asset foundation those workflows run on is not completely trustworthy? When the metrics your team presents are an informed guess, not a defensible fact? When a ghost asset, a duplicate record, or a stale asset gets amplified by AI-assisted workflows, and the error compounds before anyone catches it? The actionability era has exposed the next problem: you can’t act at scale on data you can’t verify. It’s true for your team, and for your AI agents.
At Adapt 2026, we’re addressing that challenge directly. Across the Axonius Asset Cloud, we’re shipping features that extend asset intelligence further — into new asset types like cyber-physical assets, into organizational structure, into the data layer itself — and establishing a verified growth truth as the foundation security programs run on. Asset intelligence built for human judgement, ready for machine action.
Here’s everything we’re announcing this week across the Axonius Asset Cloud.
Axonius AI: Remediation recommendations your team will actually use
AI acting without the truth is just guesswork. That’s the core premise behind Axonius AI, and the reason the asset foundation matters as much as the AI capabilities built on top of it. Axonius AI operates in two dimensions: using AI to make security teams faster and more effective, and helping security teams get visibility into how AI is being used across their own environments.
The first delivers capabilities like AI-powered remediation recommendations and automation that draw on the full context of your assets, security findings, and business context — not a black box model working from partial signals.
You’ll see Axonius AI in the platform starting with Axonius AI Recommended Actions, generally available early May, which surfaces specific remediation steps for each finding, ranked by expected impact, and followed by a rapid expansion to mitigations (applying the same principles to mitigating controls) in June.
_2.png)
Example of AI-recommended mitigation. By enabling ASLR Bypass Prevention in Falcon Prevention Policy in CrowdStrike, you can mitigate over 76k security issues across 436 devices.
Stay tuned for more on Axonius AI in the upcoming weeks.
What’s new in Axonius Cyber Assets
Axonius Verified Assets: Asset inventory without the fine print
Every security team has a number it uses to represent asset coverage. And almost universally, that number is not fully defensible. When unverified asset data drives security workflows and reporting, bad data doesn’t stay isolated. It propagates. An unverified record in your asset foundation creates a bad decision downstream, and at scale, those bad decisions compound.
_1_(1).png)
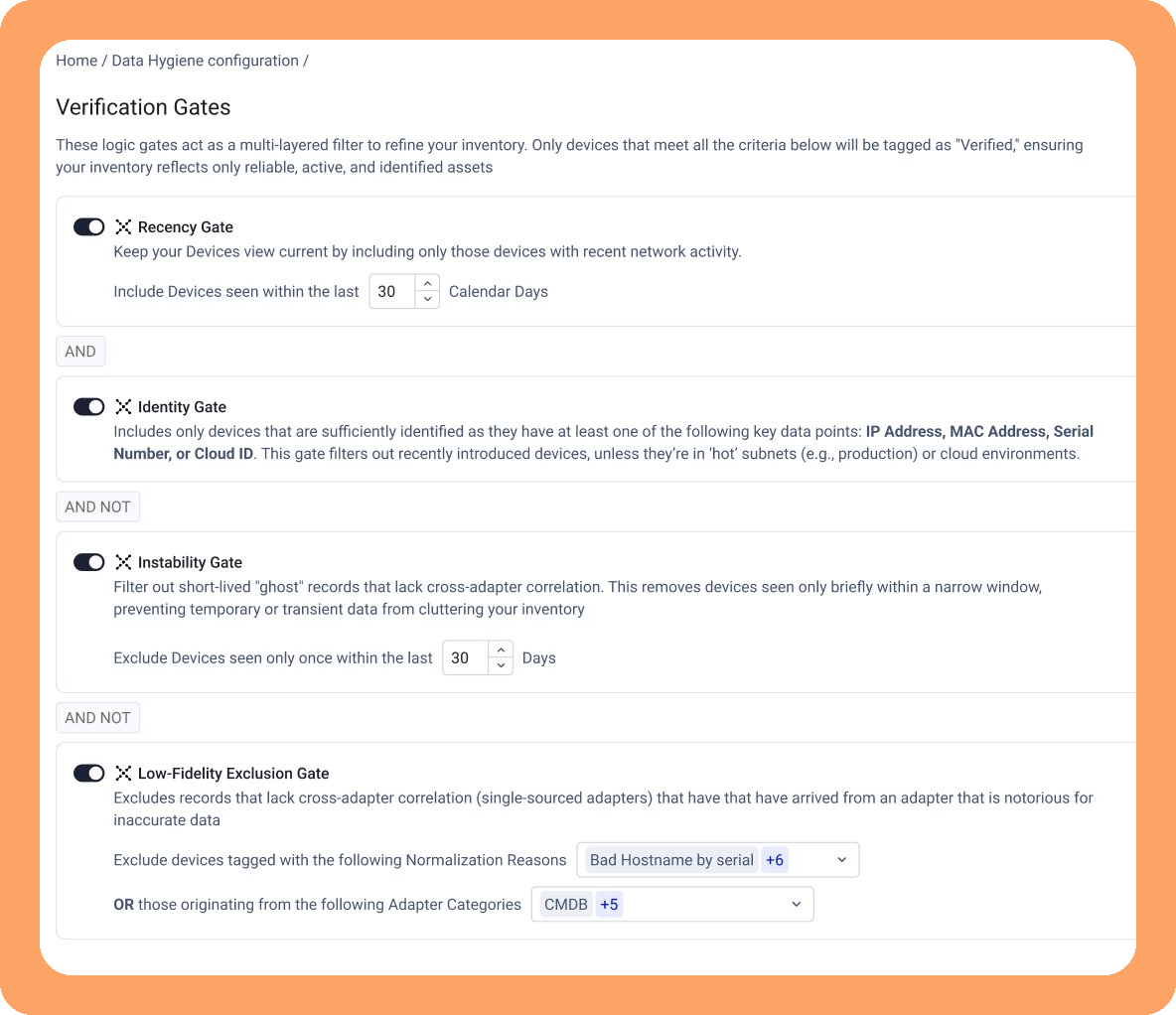
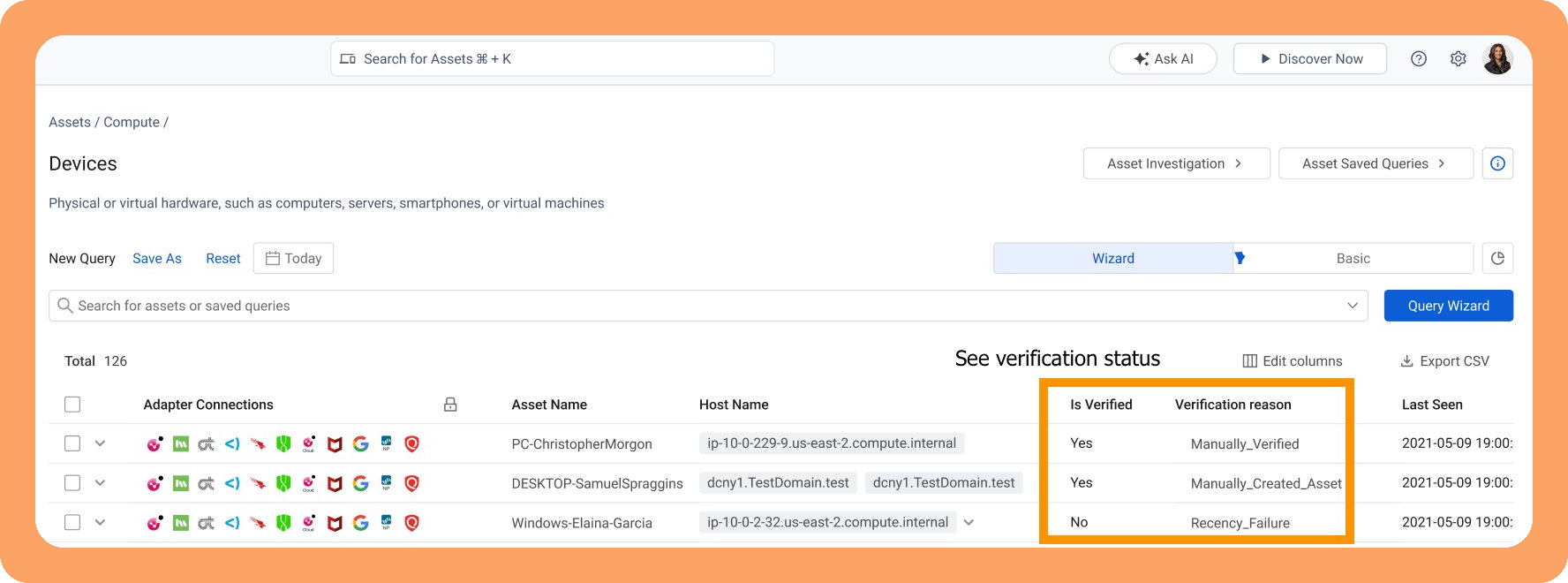
Axonius Verified Assets addresses this directly.
The premise is straightforward: not all assets in an environment are equal from a data quality standpoint. Some records are recent, corroborated across multiple sources, and stable. Others are ephemeral, potentially stale, or carry duplicate risk. Axonius Verified Assets evaluates every asset against a defined set of quality gates — recency, device identity, source stability, and data integrity — to produce a trustworthy result.
Assets that pass the quality gates are tagged as Axonius Verified and surfaced as such in the platform. These are assets you can act on with confidence: use them to feed automated workflows, build risk models on top of them, and include them in your metrics reporting. The Axonius Verified tag is the signal that the data has been validated, not just collected.
Assets that do not pass the quality gates are not immediately discarded; those are routed to a triage dashboard with more detailed failure analysis, so that gaps get fixed rather than forgotten. Why is this important? The goal isn’t a smaller inventory, it’s a trustworthy one.
Decision-grade asset intelligence requires decision-grade data. And decision-grade data requires verifiable truth. Axonius Verified Assets is where that starts.
Asset inventory updates: Org-level context, fewer blind spots
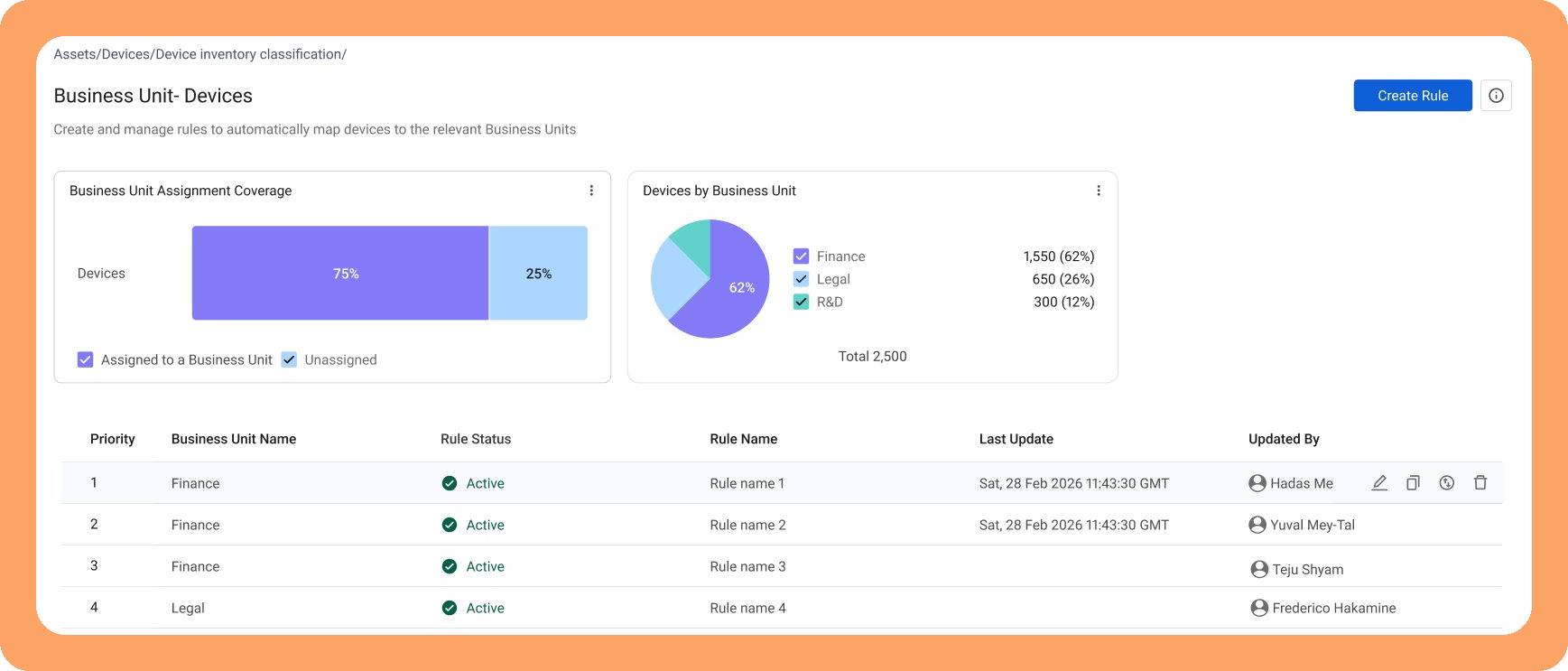
Security programs tend to run on asset characteristics that are not standardized across asset management platforms. Is this Windows endpoint duplicated? Does it belong to Finance or Engineering? Until now, teams have been answering those questions in Axonius through workarounds: custom fields, informal tagging conventions, and naming schemes that don’t work at an organizational scale. Updates to asset inventory fields formalize those categories as first-class characteristics.
Lifecycle states give teams a structured way to define where an asset stands: active, retired, managed, unmanaged, in-scope, or out-of-scope for a specific policy. These states are visualized in dashboards and usable as filters across the inventory, including as inputs to downstream workflows like CMDB reconciliation.
Now, Asset Enrichment introduces characteristics like business units, asset lifecycle state, and asset criticality — drawn from adapters connected to Axonius — so that users can filter to their slices of the inventory instantly. These characteristics can then be used for faster querying and dashboard creation.
What's new in Axonius Exposures
The threat landscape continues to evolve rapidly, yet 55% of companies are still tracking remediation in spreadsheets, per the Axonius 2026 Actionability Report. Security teams struggle with the gap between “known” and “fixed”: the coordination overhead, unclear ownership, and prioritization models that create a drag on efficiency and don’t reflect real business risk.
This week, we’re shipping new Axonius Exposures features designed to reduce that drag to zero: Security Findings Rules that extend coverage beyond CVEs to any policy-defined condition, improved out-of-the-box risk scoring with asset and business context built in, and Remediation Ownership that assigns every finding an owner with defined SLAs from day one.
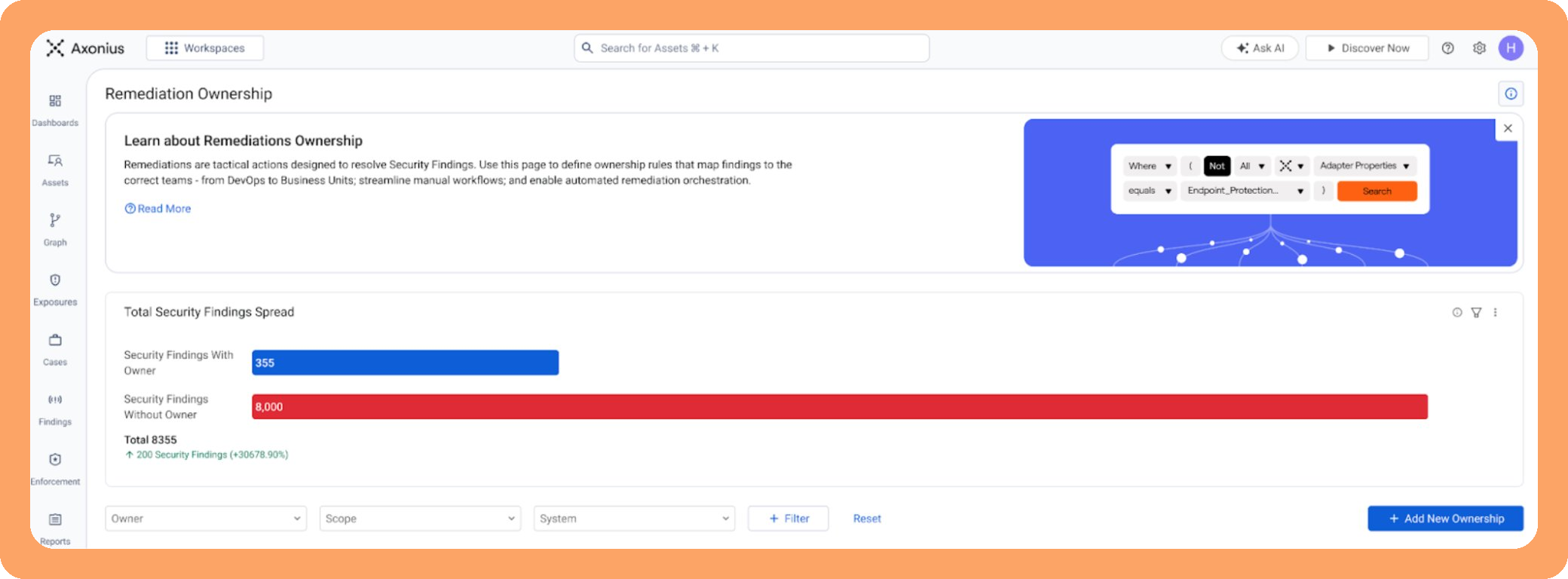
For the full breakdown, including how Attack Path Analysis and AI-Powered Recommended Actions work, read the full Exposures overview.
Axonius Cyber-Physical Assets: Now in Early Access
Factories, hospitals, logistics operations, and smart buildings run on devices that traditional security platforms weren’t built to manage. These cyber-physical systems are frequently “invisible” to standard asset inventories, often because they can’t run agents, don’t rely on traditional scanning approaches, and operate on protocols outside what most security tools understand.
Stemming from our Cynerio acquisition, Axonius Cyber-Physical Assets (CPA) brings these environments into the Axonius Asset Cloud through network-based discovery combined with deep device fingerprinting. By observing real communication behavior, CPA builds a detailed inventory of OT, IoT, and other cyber-physical assets.
These assets are then correlated into the same asset graph that already connects IT, cloud, SaaS, identities, and exposures, extending visibility across the entire environment.
The result is not just visibility, but context. Security teams can understand how cyber-physical devices interact with the rest of their environment, what they communicate with, what vulnerabilities or exposures may exist, and how they contribute to the broader attack surface. This enriched intelligence can then inform existing security workflows and reporting, helping teams make more informed decisions in environments where disruption is not an option.
Cyber-Physical Assets is in Early Access now. For the full story on how we built it and what it can do, learn more about Axonius CPA here.
_1_(1).png)
What's new in Axonius Software Assets
Outdated software is one of the most preventable sources of risk — and one of the toughest to address at scale. Security teams know they need a unified software inventory to enforce version standards, but without a clear picture of what’s running and how far behind it is, policy stays aspirational.
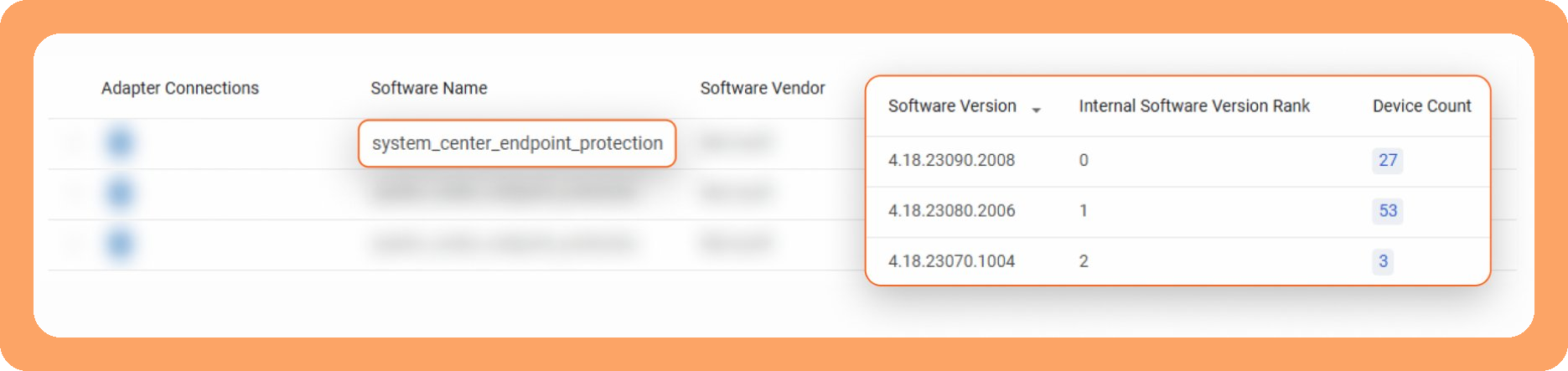
Axonius Software Assets already eliminates discovery noise to deliver a decision-grade inventory of your software estate, and this week, we’re introducing Software Version Ranking. The platform ranks all versions of a discovered software title, assigning Rank 1 to the newest version, Rank 2 to the second-newest, and so on. This allows security teams to move beyond discovery to active policy enforcement: mandating, for example, that no installed software lags more than “N-2” or “N-3” versions behind the latest discovered release.
These new Version Ranks are available to the Axonius Action Center, where security engineers can craft automations to notify users that an update is needed, open tickets to escalate a discovered drift, and more. Security and IT can work together to right-size and consolidate the software estate.
By connecting Version Rank to automated orchestration, Axonius ensures that "N-x" policies are not just monitored, but actively enforced across the entire infrastructure. The result is immediate visibility into software configuration drift, with the tooling to act on it before it becomes an audit finding or an open door for threat actors.
Platform Updates
Workflows updates: Test before you deploy
The Action Center includes advanced Workflows to help teams automate actions across their security program. With this release, we’ve added the ability to test a Workflow before it ever runs in production, giving users the confidence to move from simulation to prod. Within the Workflow builder, you can initiate a test run, enter simulated data, and step through each stage to verify the output.
Think of it as a “what-if” environment: run your logic against a test case, see where it succeeds or breaks, and fix the issues before the Workflows touches a live environment. For teams troubleshooting complex or multi-step automations, this is a significantly faster debugging path than the current cycle of run, investigate, repeat.
Dark mode and navigation redesign
Dark mode is now available across the platform. The best updates are the ones that make you wonder how you ever worked without them, and dark mode is one of those. We’ve also revamped navigation, with a structure organized around real user workflows: seeing the problem, understanding risk, then taking action. That’s the order security work happens in, and the platform now reflects it.
Bringing it all together
Each of the Axonius Asset Cloud updates here addresses a specific friction point. Workflows updates accelerate troubleshooting. Verified Assets gives you an asset foundation you can defend. Asset Enrichment makes your inventory effective at scale. Exposures closes the loop from finding to fixing.
The standard we’re building to: asset intelligence your team can defend, and your workflows depend on. The same verified asset foundation, whether a human is approving the decision or an agent is executing on it.
See everything new across the Axonius Asset Cloud.
Categories
- Axonius News

Get Started
See how to make asset intelligence actionable with a guided demo:
- Stop chasing data — work from one asset model your entire team can trust.
- See what's exposed before it's a problem — surface coverage gaps automatically.
- Turn alert noise into action — cut thousands of alerts down, to the ones that matter.
