Despite all your tools, exposure management still stalls (We fixed that)

Ori Azgad
Director of Product Management, Axonius

Shimon Tzahi
Principal Product Manager, Axonius

Stav Mor
Product Manager, Axonius

Yotam Katz
Senior Product Manager, Axonius
The security risk that disrupts your team on Tuesday should be closed by Friday. That's the ideal. Most security teams aren't there yet: not for lack of security tools, but because these tools are not built to work together at speed.
Security teams spent years building their stack. Scanners, CSPM platforms, identity management, EDRs, ZTNAs, SIEMs, Posture Management, ticketing systems. Despite that, most still can't answer the two questions that define whether exposure management is working:
What are the security issues across my attack surface right now?
Which ones do we fix first, who owns them, and what steps do they take to remediate?
Without both, the process stalls. The lack of visibility undermines confidence, and the operational drag kicks in: unclear priority, missing owners, no path from finding to fix.
At Adapt 2026, we're shipping new Axonius Exposures capabilities to deliver zero-drag defense, eliminating the operational friction that undermines confidence and delays remediation.
Here's what's new:
Security Finding Rules: Your business logic, your findings
A security finding isn't just a CVE or a generic lack of security control. It’s also a collection of security risks unique to your organization's security policy and risk profile.
Depending on your business, the lack of Yubikeys as a factor might be okay for a contractor at low risk (not worth the extra cost and risk of lost keys). For a C-suite executive, it's a critical requirement. An unencrypted volume in development might be acceptable. The same in a system containing sensitive data or a remote worker's laptop is not.
And for many programs, the most important findings don't come from a scanner at all: they live in identity hygiene, certificate management, code repositories, or the policy your team wrote last quarter requiring every SaaS application with PII to transfer data only over mTLS.
Most exposure management solutions are built to handle CVEs. Anything else — non-CVE findings, policy-defined conditions, posture mismatches, etc. — your team is still on the hook to identify and track manually.
Security Finding Rules closes that gap. Security findings in Axonius cover what your program and environment actually demand, not just what your scanner can see. And they inherit the full Exposures workflow: status tracking, risk scoring, ownership assignment, and remediation actions.
How it works: Security Finding Rules can now come from three sources: built-in definitions from Axonius, data surfaced by your adapters, or custom rules defined by your team. Define a query in Axonius that returns assets matching a condition. Promote that query to a Security Finding Rule. And that’s it: your exposure management program is tuned to your policy.
This works across all 40+ asset types and 1,400+ adapters supported by Axonius, so you can manage all exposures in one place.
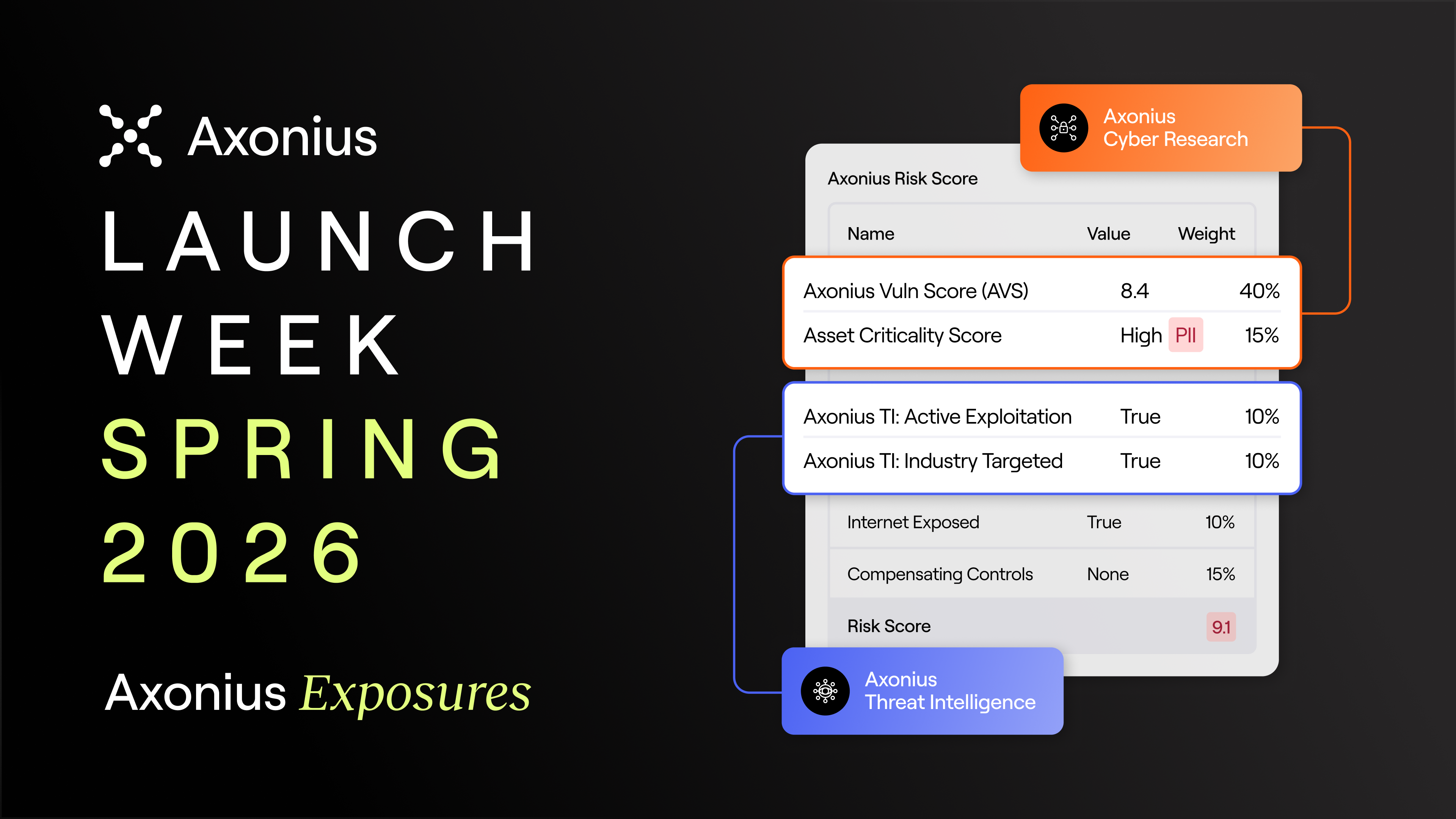
Risk scoring: Prioritization that reflects your environment
Axonius customers have seen real results from the Axonius Risk Score: a model that brings asset context, security data, and business context into a single number. Priority reflects actual business risk, not raw CVSS scores or black box risk models that don't reflect your reality or make you look clueless in front of stakeholders when defending why a risk is urgent.

The friction has been getting started. Building a risk model that reflects your environment requires a baseline. Even more: many teams can greatly benefit from a threat intelligence source, but that adds extra costs to their stack.
We're removing those barriers with three predefined, research-backed scores applied by default:
Axonius Vulnerability Score (AVS) aggregates vulnerability sources and threat intelligence with explainable AI (XAI) to surface risk aggravators and mitigators in plain English: so every vulnerability comes with the reasoning that turns pushback into action.
Asset Criticality captures the business importance of each asset based on its characteristics, like type, connectivity, and function (i.e., if it's a DHCP server or an asset that belongs to a critical user). If the affected asset is critical to your operations, that shows up in the score.
Axonius Threat Intelligence brings up-to-date external signals (known exploited vulnerabilities, adversary targeting data, and active exploitation likelihood) into fully connected to your assets, security findings, and risk score. That gives you intel instantly contextualized to your assets without the need for a third-party threat intel feed.
These improvements, together, give you risk scores including asset, business, and security context from day one. The floor is higher than where a score built solely on scanner output leaves you. Customize from there.
Attack Path Analysis adds one more layer: if a finding is reachable from the internet through a known attack path (including through on-premises networks), that context surfaces on the finding. Reachability changes priority. Now it's visible before the attacker makes it visible for you.
Remediation Ownership: Reach zero mean time to ownership
Here's what unclear ownership looks like on a Tuesday afternoon:
A critical security finding lands in your queue. The listed owner left three months ago. You Slack the infrastructure team. No response by end of day. You escalate. Their manager says: “Try the platform team”. Email sent. Three days later, someone answers: it might be DevOps. You're running a Zoom call with three teams, each convinced the issue belongs to someone else.
You're holding the finding. You're asking people to take on unplanned work. You make the case for why it matters. Weeks pass. The finding is still open, and the SLA is overdue.
This is what happens when ownership information is based on siloed information and security asking favors versus concrete rules aligned with business and asset data.
The rule that replaces that process: Remediation Ownership uses the information that powers the Axonius risk score (asset, business, and security context), including business function, team structure, and organizational data from the HR and identity systems already connected to Axonius to map who owns a security finding.
.png)
With remediation ownership, every finding gets a remediator with defined SLAs. 100% ownership rate. Near-zero mean-time-to-ownership. A pre-defined rule that says "this is yours, here's the deadline" with unshakable confidence instead of "does anyone know who owns this?"
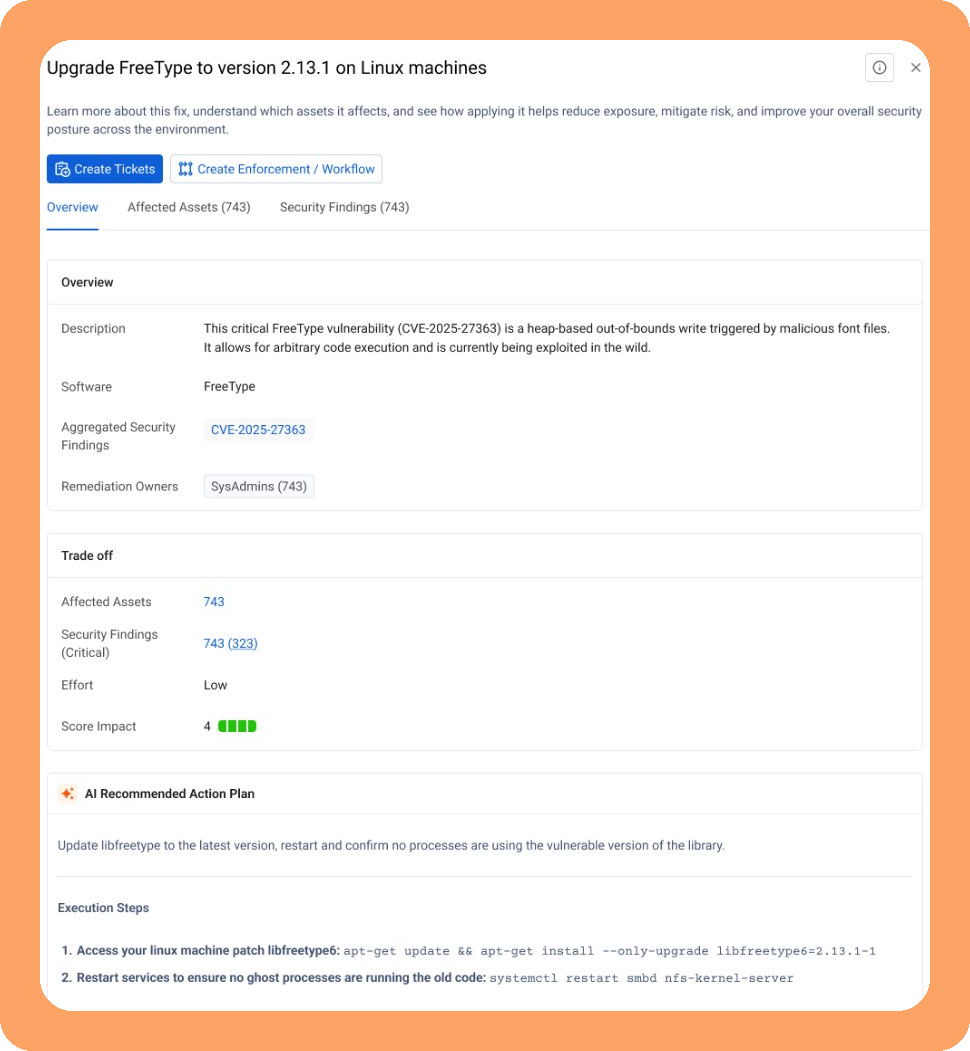
When ownership is clear, the next hurdle is to make sure the remediator knows what to fix and how to do it. With Recommended Actions, Axonius AI surfaces the highest-impact remediation steps ranked by expected impact: for that finding, on that asset, in that environment. When a permanent fix needs time, Recommended Mitigations adds interim risk reduction steps so exposure doesn't wait on a patch cycle.
What exposure management has been missing
Exposure management should be straightforward. Every finding should surface the moment it exists. Every risk score should reflect the actual business value of what's being protected, in a way you can explain to the business (not an opaque score). Every finding should have an owner the moment it's identified. Every remediator should know exactly what to do and have the tools to do it. Every security pro should spend more time doing security, not covering silos and tool deficiencies.
That's not an unreasonable ask. This is how security should work in the first place.
The gap between the ideal world and what security teams end up doing to cover silos is driving security burnout. Most security tools were built to answer one question well: what's broken on this asset? That scope is right for defense-in-depth, but it's an incomplete answer for defense in breadth.
When your assets span different types and environments, when a security risk in one system creates lateral movement to another, a single-source model runs out of signal. It can't score based on what it can't see. It can't assign owners from systems it isn't connected to. It can't recommend actions for asset types it wasn't built to track.
Software Analyst Cyber Research (SACR) Market Guide: “What we now focus on is probably 5-10% of what we told remediators to worry about in the past.” – Axonius customer
Latio Tech (2025): "Axonius is leading due to their robust mapping of vulnerabilities across various asset and identity types."
Axonius Exposures is built for this expanded scope. To expand your defense-in-depth to uncover findings, asset types, and operational workflows they leave untracked (and your team is paying with manual work).
What's the value when you bring this all together?
Each capability removes a specific drag point. Together, they change the operating model.
Increase speed: When security findings are aggregated automatically, owners are assigned with remediation steps surfaced immediately, and proactive steps are taken via automation, the coordination overhead collapses. Findings don't wait days to be discovered or for someone to claim them. Remediators don't wait for someone to tell them what to do. The time from "found" to "assigned and actioned" shrinks from weeks to hours.
Reduce risk: When risk scores factor in asset exposure, business criticality, and out-of-the-box threat intelligence, you're prioritizing what truly matters, not what's technically severe.
Increase productivity: Security practitioners spend their time fixing security problems, not managing silos. The work to compensate for risk silos that consumed their week (spreadsheets, Slack threads, passive-aggressive emails, ownership negotiations, custom scoring models) moves to the platform. What's left is the work they were hired (and love) to do.
Future proof of the process: Security protects an environment that constantly changes, and needs to quickly adapt to new asset types, changes in security tools, and absorbing business changes like M&A. Exposures is built for that: whether the change is on what you need to protect or what security tools you use, you can absorb changes without having to rebuild your entire exposure management process.
The outcome: a security team that operates with zero drag — at the speed of the threat, not the speed of the spreadsheet.
See Axonius Exposures in action
The finding that stalls on Tuesday should close by Friday. Book a demo to see the difference Axonius Exposures can make for your team.
See everything new across the Axonius Asset Cloud.
Available now: Security Finding Rules, Axonius Status, Risk Score Normalization, OOTB Risk Score, Axonius Vulnerability Score, Asset Criticality. GA with May updates: Threat Intelligence enrichment, Attack Path Analysis, Remediation Ownership, Recommended Actions. Early Access (GA by July): Recommended Actions: Mitigations. Full details in our product documentation.
Categories
- Axonius News

Get Started
See how to make asset intelligence actionable with a guided demo:
- Stop chasing data — work from one asset model your entire team can trust.
- See what's exposed before it's a problem — surface coverage gaps automatically.
- Turn alert noise into action — cut thousands of alerts down, to the ones that matter.
